rfid protection for servers Passports and some credit cards have RFID chips that allow information to be read wirelessly. An industry has sprung up to make wallets and other products that block hackers from "skimming" . So, have Wired/Bluetooth switch pro controller connected to pc, use its nfc reader/writer to .
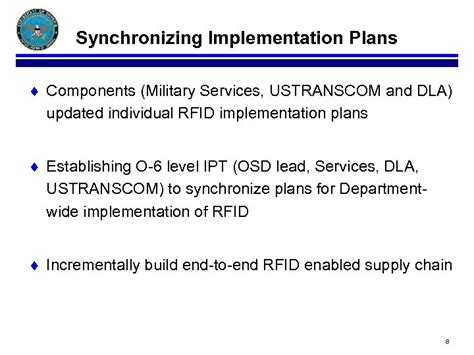
0 · rfid ustranscom
1 · rfid tracking portal
2 · rfid systems for small business
3 · rfid server rack tags
4 · rf itv server
5 · itv server
6 · army rfid tracking
7 · army rf itv
Here’s how you can read NFC tags with your iPhone: Activate NFC Reader Mode: Ensure that your iPhone is in NFC reader mode, allowing it to detect and interact with nearby .
Passports and some credit cards have RFID chips that allow information to be read wirelessly. An industry has sprung up to make wallets and other products that block hackers from "skimming" .Let's explore the top 10 challenges and vulnerabilities organizations must address to ensure the security and integrity of their RFID infrastructure. Passports and some credit cards have RFID chips that allow information to be read wirelessly. An industry has sprung up to make wallets and other products that block hackers .Let's explore the top 10 challenges and vulnerabilities organizations must address to ensure the security and integrity of their RFID infrastructure.
RFID tags can be used for tracking packages in the mail or goods in a warehouse. The RFID tag can contain tracking information or just a unique identification code. Modern . So how can you protect your sensitive data from falling into the wrong hands? In this article, we’ll discuss how uninvited parties might try to get ahold of your information and .
RFID blocking is the process of making your RFID-enabled device resistant to unauthorized access. The most popular way to achieve this is by getting an RFID blocking . RFID can automatically communicate critical information about assets, and businesses rely on RFID systems to accurately track assets, prevent loss or theft, and improve .
vehicle windshield rfid tag
To protect your RIFD database, make sure you mitigate database related vulnerabilities and risks. Despite being a target of some common attacks, RFID is gaining popularity in certain areas .
The best way to prevent eavesdropping is to adopt a layered security approach that prioritizes encryption and secure authentication protocols. Managers should ensure every . In this blog post, we’ll discuss the types of attacks that can be performed against an RFID-based access control system, as well as a few ways to protect against such attacks. . This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world .
Passports and some credit cards have RFID chips that allow information to be read wirelessly. An industry has sprung up to make wallets and other products that block hackers .
Let's explore the top 10 challenges and vulnerabilities organizations must address to ensure the security and integrity of their RFID infrastructure. RFID tags can be used for tracking packages in the mail or goods in a warehouse. The RFID tag can contain tracking information or just a unique identification code. Modern . So how can you protect your sensitive data from falling into the wrong hands? In this article, we’ll discuss how uninvited parties might try to get ahold of your information and .
RFID blocking is the process of making your RFID-enabled device resistant to unauthorized access. The most popular way to achieve this is by getting an RFID blocking . RFID can automatically communicate critical information about assets, and businesses rely on RFID systems to accurately track assets, prevent loss or theft, and improve .To protect your RIFD database, make sure you mitigate database related vulnerabilities and risks. Despite being a target of some common attacks, RFID is gaining popularity in certain areas .
The best way to prevent eavesdropping is to adopt a layered security approach that prioritizes encryption and secure authentication protocols. Managers should ensure every .
In this blog post, we’ll discuss the types of attacks that can be performed against an RFID-based access control system, as well as a few ways to protect against such attacks. .
rfid ustranscom
vault card rfid
rfid tracking portal
rfid systems for small business
some locks have NFC readers built in, but that’s just a convenience. You can .
rfid protection for servers|rfid server rack tags